When traditional sectors need modern tools
- Biju Paul

- Dec 11, 2019
- 3 min read
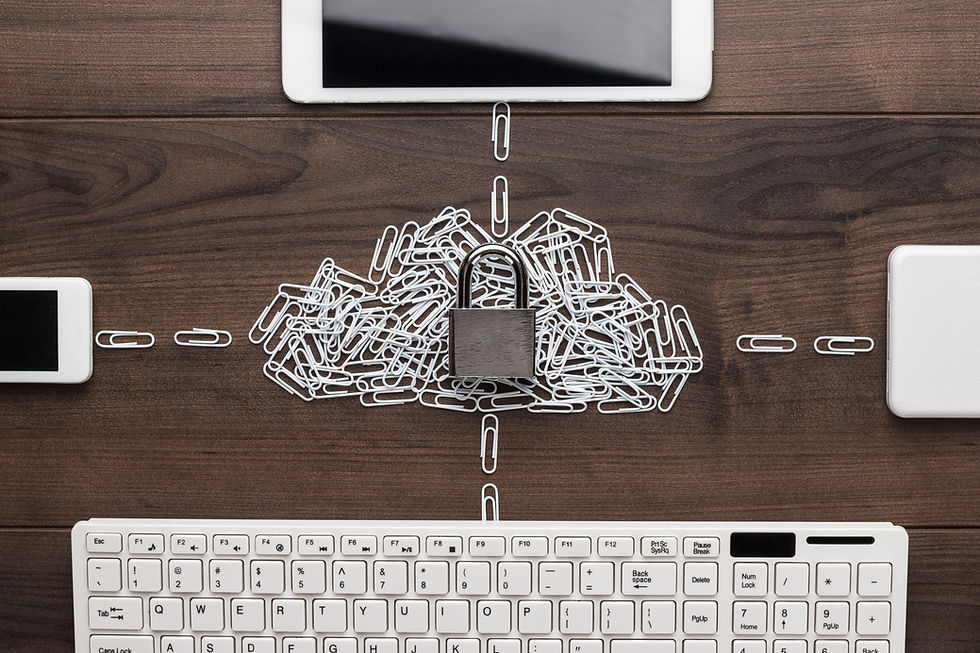
Several traditional sectors including manufacturing, mining and heavy industries continue to face cybersecurity threats. Awareness of protecting the critical assets and developing a wholistic cybersecurity cover is the need of the hour
Given the nature of certain industries such as manufacturing, mining & metallurgy, heavy industrial equipment and construction, the technology and digital infrastructure are often scattered and de-centralised. This exposes them to several kinds of cyber threats. While such organisations are already looking at improving their cybersecurity framework, a majority of them are still exposed to several kinds of threats.
Consider some examples to understand the threats: A heavy industrial equipment manufacturer is prone to such attacks due to various open-source network in the entire machinery. A mining and metallurgy firm may face a security breach in its data repository, which may be sensitive. It is often seen that output-heavy industries also have governments as stakeholders. The government’s intervention makes it even more susceptible to threats and attacks. The wealth of information in the hands of cybercriminals can be a weapon. Failing to meet the security standards will, therefore, result in tens of millions of dollars!
Hence, enterprises comprising of old and new networks and devices have higher chances of attracting cybercriminals. Clearly, the traditionally run enterprises have the following vulnerabilities:
T
here are fewer layers of protection in terms of a firewall.The enterprises have a lesser number of IT expertise and therefore, lower levels of awareness against cyberattacks.These lack in terms of cybersecurity policy.
How can these organisations protect themselves from cyberattacks?
First, it is important to identify all potential assets and provide a security net for all of these assets.Second, with customisation of assets, an integrated security network can be developed.Third, there is a need to develop a holistic cybersecurity strategy.
Let us look at these steps in detail:
1) Identifying potential assets: Eliminating the complexities of the network is the initial step in identifying potential assets. Amidst a wider range of possible targets within the entire infrastructure, it is easier to identify those critical assets which are often vulnerable to cyberattacks. An attack simulation and exposing the infrastructure to real-world challenges will make the identification easier.
2) Customization of the security network: The customization process starts right from the stages of the initial installation of the systems and infrastructure. The traditional machinery of the company is process bound to certain specific manufacturing/output requirements. Hence, customization from time-to-time, depending upon the evolving nature of threats should go hand-in-hand. Traditional businesses can thus opt to customize the security patterns on all parts of the network, including mobile applications, where data breaches can happen easily.
3) Developing a holistic cybersecurity strategy: Finally, keeping in mind the critical components, customized network security and vulnerable assets, a cybersecurity strategy can be planned and prepared. Few things need to be kept in mind while devising the policy:
a) Awareness is the key to success. Hence, devising a detailed policy framework makes it easier to comprehend and follow. All employees and departments should be made aware of these challenges.
b) The strategy must clearly describe the threats to critical and non-critical assets. A flexible and evolutionary approach is best suited. Hence, there is a need for regular upgrades. Keeping in mind the evolving nature of the cyber world makes the transformation easier.
c) In such a scenario, identifying individual/departmental responsibilities is of importance here. This can be done through a townhall, regular meetings with the CTO and external cybersecurity experts and consultants.
Complexity is the new reality of large, archaic companies, re-inventing themselves against cyber-related frauds and attacks. The inter-connected devices, networks can be a problem for these companies. But the same can become an important element in the solution that the industry is currently trying to find.




Comments